CRIMP / Resource Library
Intelligence Guides for Critical Infrastructure
Seven in-depth guides on how OSINT-led intelligence protects Australia's most critical assets — written for the operators, security teams, and programme managers responsible for defending them.
All Guides

When the Supply Chain Is the Target
How activist campaigns are mapping and attacking Australia's defence industry
Activists have mapped the F-35 supply chain. They know which ports handle which components, which shipping companies move parts between manufacturers, which airports process outbound shipments. At Rosebank Engineering in Bayswater, Victoria, eight people climbed the factory roof at 6am and refused to come down for over twelve hours.

No Safe Transfer
Intelligence for freight security across air, rail, and road
Organised cargo crime doesn't respect the difference between an airside terminal, a rail corridor, and a road distribution hub. It follows the cargo. The intelligence picture needs to do the same.
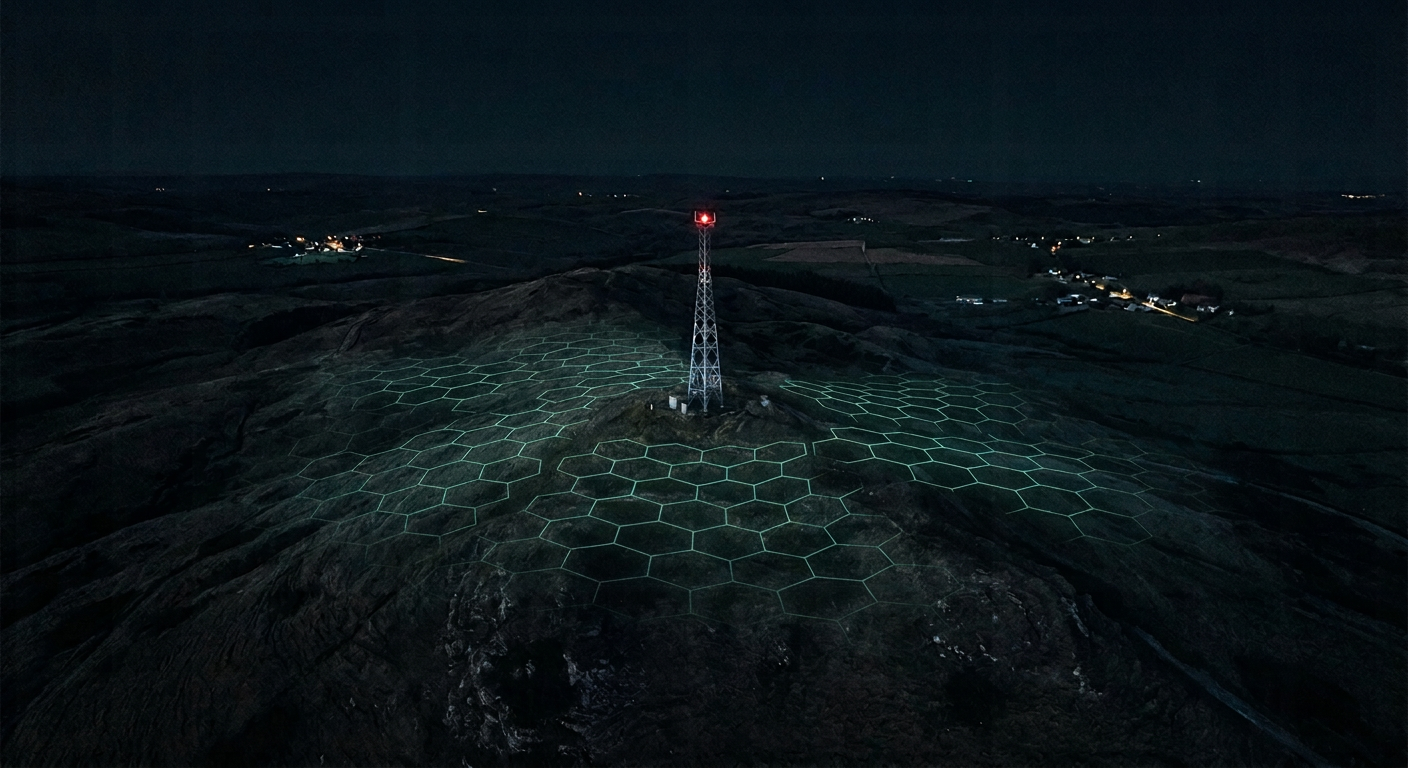
Defending Telecom Infrastructure
Protecting towers from physical threats and building a live asset picture
5G conspiracy-driven vandalism caused dozens of documented tower arsons across Australia. CRIMP monitors the online environments where these threats are planned — giving operators intelligence before anyone reaches the fence.

Monitoring What You Cannot See
Security intelligence across mines, parks, and water catchments
Camera grids don't scale to a Pilbara mine or a national park the size of a small country. Australia's wildlife makes false positives a strategic problem. The answer is intelligence, not more cameras.

The Threat Already Inside the Fence
Managing insider risk with geospatial and online intelligence
The SOCI Act mandates personnel security as a mandatory risk management domain for good reason. Geospatial boundary signals, online behaviour, and dark web monitoring together create the correlated picture that makes insider risk visible.

When the Threat Is Public and Coordinated
Intelligence-led preparation for planned operational disruption
Activist campaigns targeting Australian critical infrastructure are organised publicly — on social media, event platforms, and open forums. The intelligence to prepare is already there. The question is whether anyone is reading it.

Sabotage in Waiting
Detecting state-sponsored sabotage preparation against Australian infrastructure
In November 2025, ASIO Director-General Mike Burgess warned that state actors have moved from espionage to active sabotage preparation — mapping vulnerabilities in Australia's energy and telecom systems to enable destructive attacks in a future conflict.
Ready to Protect What Matters?
See how CRIMP gives your team the intelligence picture to stay ahead of every threat type covered in these guides.
